Cybersecurity researchers have uncovered a powerful new mobile spyware toolkit called ZeroDayRAT, now being sold through Telegram channels to cybercriminals worldwide. Unlike typical malware focused only on stealing data, this platform gives attackers full remote visibility into a victim’s phone, including location tracking, camera access, financial information, and live monitoring capabilities.
Security analysts warn that the tool lowers the barrier to entry for sophisticated mobile attacks, making advanced surveillance techniques accessible to ordinary cybercriminals.
📱 A Cross-Platform Spyware Designed for Full Device Control
ZeroDayRAT is built to work across a wide range of devices, supporting Android versions from 5 up to the latest releases and iOS versions as well. The malware is typically spread through social engineering tactics, malicious links, or fake app stores that trick users into installing infected applications.
Once installed, the spyware connects to a remote control panel hosted on the attacker’s own server. From there, operators can view detailed information about the compromised device, including:
- Device model and operating system
- Real-time location and movement history
- SIM and carrier details
- Battery status and activity
- App usage patterns
- Notifications and recent messages
This data allows attackers to build a comprehensive profile of the victim’s behavior, contacts, and routines.
🛰️ GPS Tracking and Account Harvesting
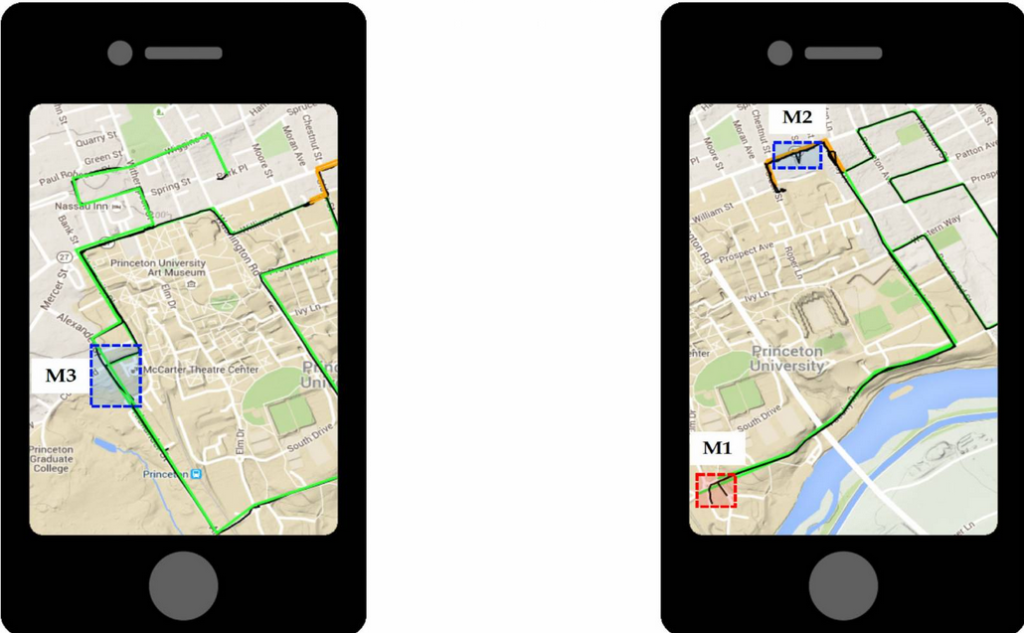
One of the platform’s most invasive features is continuous location monitoring. The spyware collects GPS coordinates and maps them over time, effectively turning the infected phone into a tracking device.
The system also scans for accounts linked to the device. Email addresses, usernames, and services tied to social media, messaging apps, e-commerce platforms, and streaming services can all be exposed, giving attackers valuable intelligence for further exploitation or identity theft.
🎥 Live Surveillance: Camera, Microphone, and Keystrokes
ZeroDayRAT goes beyond passive data collection. It allows attackers to actively spy on victims in real time.
Capabilities include:
- Live camera streaming
- Remote microphone activation
- Keystroke logging
- SMS interception
- Capture of one-time passwords (OTPs)
By collecting authentication codes and passwords, attackers can bypass two-factor authentication protections and gain access to sensitive accounts.
💰 Targeting Crypto Wallets and Digital Payments
Financial theft is a core component of the spyware. The malware scans devices for cryptocurrency wallets and mobile payment apps, including widely used platforms for digital transactions.
One particularly dangerous technique involves clipboard hijacking. When a victim copies a wallet address to send funds, the malware silently replaces it with the attacker’s address, redirecting the transaction without the user noticing.
Banking apps, mobile wallets, and online payment services are also targeted, allowing criminals to intercept credentials or manipulate transactions.
📉 A Tool Once Reserved for Nation-State Operations
Experts say that tools with this level of capability were once associated only with government surveillance programs or highly specialized cyber operations. The fact that a turnkey solution is now being marketed openly on messaging platforms signals a major shift in the cybercrime landscape.
With minimal technical skill, a buyer can deploy the spyware and gain access to a victim’s communications, location, finances, and private life from a web browser.
⚠️ Rising Wave of Mobile Malware Campaigns
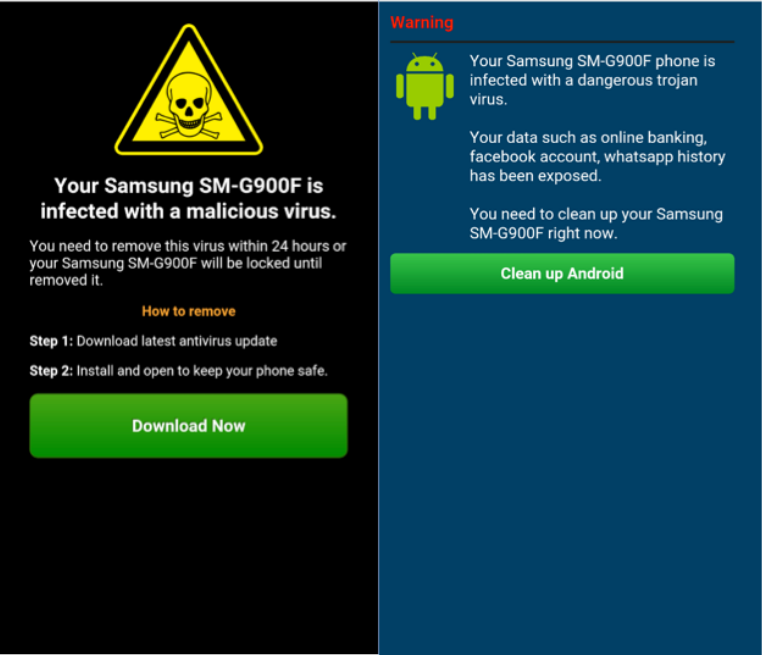
The discovery of ZeroDayRAT comes amid a surge in mobile-focused cyber threats worldwide. Recent investigations have revealed multiple campaigns using deceptive apps, phishing pages, and fake updates to infect devices.
Common tactics include:
- Malicious apps disguised as legitimate tools or games
- Fake banking or government service applications
- Phishing links delivered through messaging platforms
- Remote access scams using trusted software
- Malware hidden in unofficial app stores
Some operations even exploit features meant for enterprise deployment or accessibility services to bypass platform security protections.
💳 NFC Payment Attacks and “Tap-to-Pay” Fraud
Another emerging threat involves malware that abuses contactless payment technology. Known as NFC relay attacks or “Ghost Tap,” these schemes capture payment card data from victims’ phones and transmit it to attackers’ devices, enabling fraudulent transactions as if the physical card were present.
Security firms have documented significant financial losses from these operations, with criminal groups coordinating networks of money mules to cash out stolen funds.

🔐 Why Mobile Devices Are Prime Targets
Smartphones now store vast amounts of personal and financial information, making them highly valuable targets. They also serve as authentication devices for banking, email, and corporate systems, meaning a compromised phone can open the door to multiple accounts at once.
As mobile usage continues to grow, attackers are investing heavily in tools designed specifically for these platforms.
🛡️ Protecting Yourself From Mobile Spyware
Security experts recommend several precautions to reduce risk:
- Install apps only from official app stores
- Avoid downloading updates from links or pop-ups
- Review app permissions carefully
- Enable device security features and updates
- Use mobile security software when possible
- Be cautious of unsolicited messages or calls
🔎 The Bottom Line
ZeroDayRAT represents a new generation of commercial spyware that combines surveillance, credential theft, and financial exploitation into a single package. Its availability on underground marketplaces highlights how quickly advanced cyber capabilities are spreading beyond elite threat actors.
For individuals and organizations alike, the discovery underscores an urgent reality: mobile security is no longer optional. It is a critical frontline in the fight against modern cybercrime.