Node.js maintainers have issued emergency updates to address a serious vulnerability that can cause production applications to crash unexpectedly, opening the door to denial-of-service (DoS) attacks across much of the Node.js ecosystem.
According to the Node.js security team, the issue occurs when applications rely on async_hooks, a low-level API commonly used to track asynchronous activity such as HTTP requests, database calls, and background jobs. Under specific conditions, a stack overflow triggered by deeply recursive user input causes Node.js to terminate abruptly instead of raising a recoverable error.
What Goes Wrong
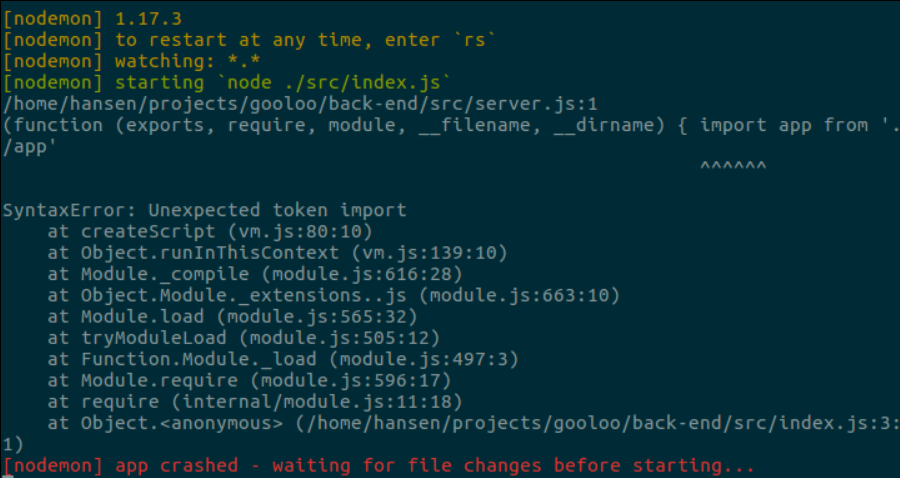
Normally, Node.js and the V8 engine attempt to recover gracefully when stack space is exhausted, allowing frameworks to catch the error and keep services running. However, when async_hooks is enabled, a bug causes Node.js to exit immediately with an internal runtime failure code, bypassing normal error handling entirely.
This means attackers can deliberately supply input that forces excessive recursion, crashing the application and taking services offline.
Why the Impact Is So Broad
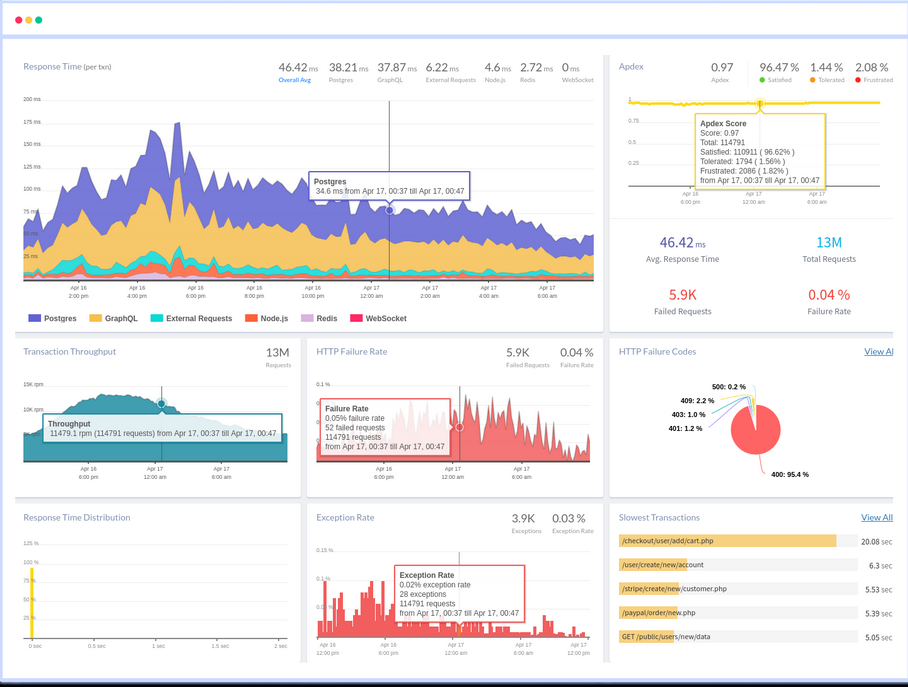
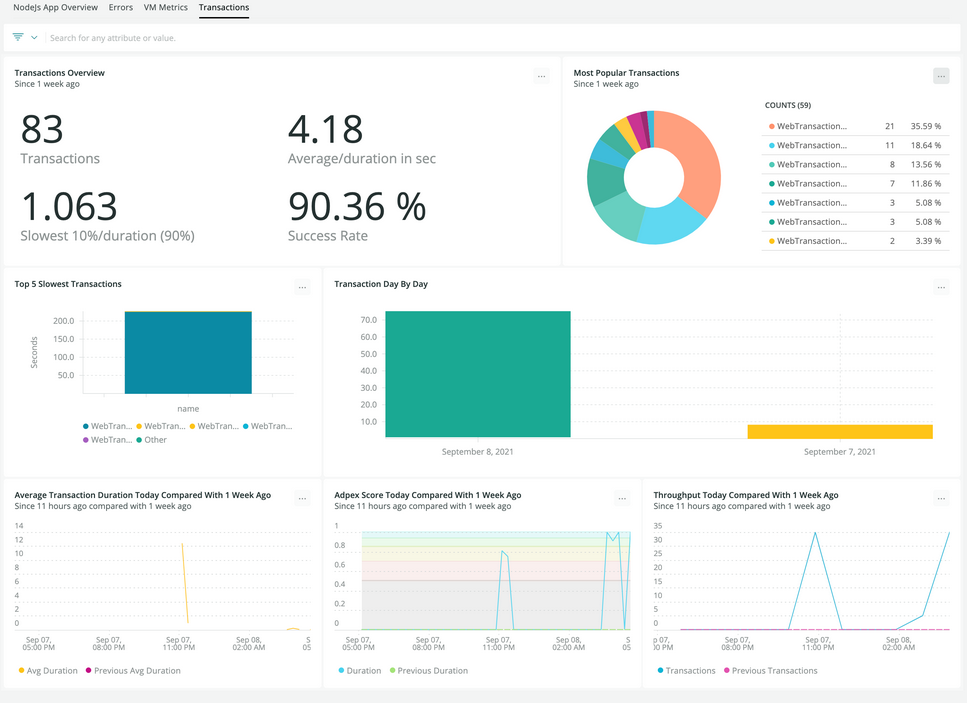
The problem affects a wide range of popular frameworks and monitoring tools that rely on AsyncLocalStorage, a feature built on top of async_hooks. This includes server-side rendering frameworks like Next.js and React Server Components, as well as many application performance monitoring platforms used in production environments.
Because these tools are deeply embedded in modern Node.js deployments, the vulnerability effectively reaches “virtually every production Node.js app,” according to the maintainers.
Affected and Fixed Versions
The flaw has been patched in the following releases:
- Node.js 20.20.0 (LTS)
- Node.js 22.22.0 (LTS)
- Node.js 24.13.0 (LTS)
- Node.js 25.3.0 (Current)
All Node.js versions from 8.x through 18.x are affected, but older releases remain unpatched due to end-of-life status.
The vulnerability is tracked as CVE-2025-59466 and carries a CVSS score of 7.5.
Why Node.js Calls It a “Mitigation”
While the practical risk is significant, the Node.js team stopped short of labeling the issue a full security fix. Stack exhaustion behavior is not formally defined in the ECMAScript specification, and the V8 engine does not treat it as a traditional security bug. In addition, Node.js’s uncaughtException handler is designed as a last-resort mechanism, limiting how safely these failures can be intercepted.
Despite this, the maintainers included the patch in a security release due to its ecosystem-wide impact and the real-world risk of service disruption.
What Developers Should Do
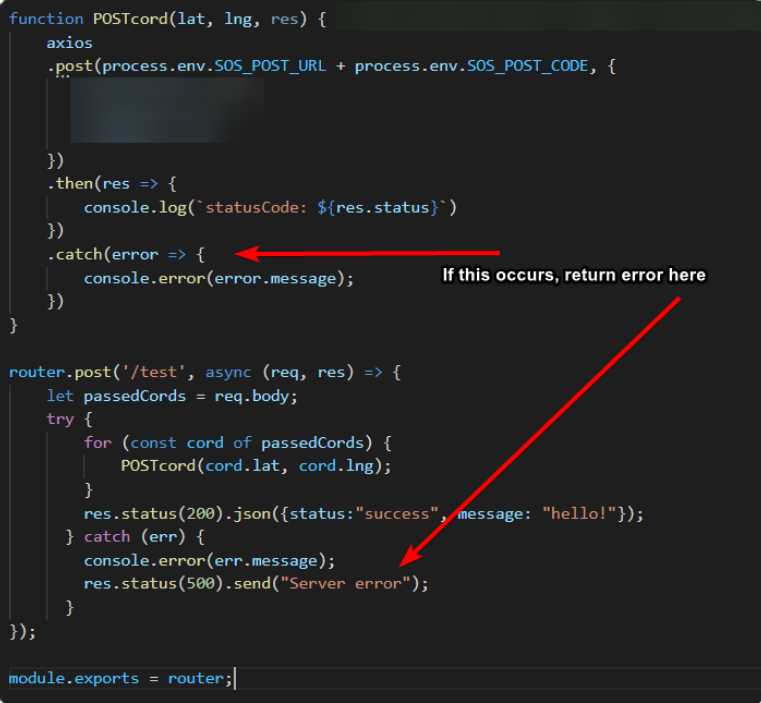
Organizations running Node.js in production are strongly advised to upgrade immediately. Framework and library maintainers are also encouraged to harden recursion handling and sanitize user input to prevent stack exhaustion scenarios.
In addition to this issue, Node.js also fixed three other high-severity vulnerabilities that could enable data exposure, file access through crafted symbolic links, or remote denial-of-service attacks.
Taken together, the updates highlight how low-level runtime behavior can have outsized consequences in modern application stacks—and why timely patching is critical for keeping Node.js services online and secure.