Security researchers have uncovered a new multi-stage phishing operation aimed at users in Russia, delivering a combination of ransomware and a remote access trojan (RAT) known as Amnesia RAT.
According to a recent analysis from Fortinet FortiGuard Labs, the campaign starts with social engineering, using business-related bait that looks harmless at first glance. Victims receive documents designed to feel normal and work-related, but these files are only meant to distract the user while malicious actions run quietly in the background.
What makes this campaign different
Fortinet highlighted two key traits that make this attack more advanced than typical phishing attempts:
- Cloud service “division of labor”
The attackers split their infrastructure across different cloud platforms:- GitHub is used to host scripts and loaders
- Dropbox is used to store the main malware binaries
- Abuse of “defendnot” to disable Microsoft Defender
A major element of the campaign is the use of a tool called defendnot, which can trick Windows into thinking a third-party antivirus is installed. When that happens, Microsoft Defender may shut itself off to avoid “conflicts.”
How the infection begins (ZIP → decoy files → LNK trick)
The attack is delivered through compressed archives (ZIP files) containing:
- multiple decoy documents
- a malicious Windows shortcut file (LNK)
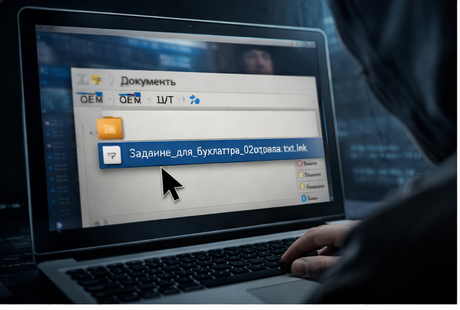
These files use Russian-language names, and the shortcut is disguised using a double extension, for example:
Задание_для_бухгалтера_02отдела.txt.lnk
This makes the file look like a harmless text document at a quick glance.
Once the victim clicks it, the shortcut launches a PowerShell command that downloads the next-stage script from a GitHub repo (Fortinet pointed to one such repo in their analysis).

PowerShell loader: stealth + distractions + Telegram “check-in”
After execution, the initial PowerShell stage focuses on stealth and deception:
- hides the PowerShell window to avoid raising suspicion
- creates and opens a decoy text file in the user’s AppData folder
- notifies the attacker through the Telegram Bot API, confirming the stage ran successfully
The loader also uses a deliberate waiting period (reported as 444 seconds) before moving forward. After the delay, the script pulls and runs a VBE (Visual Basic Encoded) payload.
This design gives attackers flexibility: they can update later payloads without changing the earlier infection step.
Obfuscated VBE stage: in-memory assembly + forced admin privileges
The Visual Basic script is heavily obfuscated and acts as the controller for the next stage. Instead of dropping obvious files, it assembles key parts in memory, reducing traces on disk.
It also checks whether it has administrative rights. If it doesn’t, the malware repeatedly triggers User Account Control (UAC) prompts, pressuring the victim to grant elevated permissions. Fortinet noted the script waits briefly between prompts (around 3 seconds).
What the malware does next: disable defenses, spy, and block recovery
Once it has enough access, the campaign performs multiple actions to weaken the system and prepare for payload deployment, including:
- adding Microsoft Defender exclusions for common directories like:
- ProgramData
- Program Files
- Desktop
- Downloads
- Temp folders
- switching off additional Defender security settings via PowerShell
- deploying defendnot to register a fake antivirus and disable Defender through Windows Security Center
- collecting intelligence about the environment (system profiling)
- running a surveillance module that:
- takes a screenshot every 30 seconds
- saves it as PNG
- exfiltrates it via a Telegram bot
It also damages user control by:
- modifying Registry policy settings to restrict Windows administrative tools
- hijacking file associations so opening certain file types displays a message telling the victim to contact the attacker via Telegram

Main payload #1: Amnesia RAT (full surveillance + credential theft)
After clearing the defenses, the attackers deploy Amnesia RAT (Fortinet reports a payload name like svchost.scr), retrieved from Dropbox.
Amnesia RAT is capable of serious data theft and full remote control, including:
Data targeted
- browser-stored passwords / cookies / autofill
- crypto wallets
- Discord
- Steam
- Telegram
- screenshots, webcam images, microphone audio
- clipboard contents
- active window titles
- system metadata
Remote control features
- list/kill processes
- execute shell commands
- upload/download files
- deploy additional malware
Data is mostly sent over HTTPS, with Telegram Bot API as a major exfil method. For larger data dumps, the actors may use external file hosting like GoFile, then forward links via Telegram.
Main payload #2: Hakuna Matata-linked ransomware + crypto clipboard hijack
The second destructive payload is a ransomware variant linked to the Hakuna Matata ransomware family. It encrypts multiple valuable file types including:
- documents and archives
- images and videos
- source code
- application/project assets
Before encryption, it kills processes that could interrupt encryption operations.
Fortinet also noted the ransomware monitors the clipboard and can silently replace cryptocurrency wallet addresses, redirecting transfers to attacker-controlled wallets.
Finally, the infection may end by deploying WinLocker, preventing normal interaction with the system.
Why this matters
Researchers emphasized that the campaign doesn’t need software exploits. Instead, it wins through:
- phishing + deception
- legitimate Windows tools (PowerShell, Registry policies)
- disabling defenses before deploying the worst payloads
Microsoft’s recommendation
Because defendnot can abuse the Windows Security Center behavior, Microsoft advises enabling Tamper Protection, which helps prevent unauthorized edits to Defender settings and reduces the chance of silent security disabling.
Related campaigns targeting Russian organizations
Fortinet’s findings come amid a wider spike in attacks against Russian companies, especially departments like HR and payroll.
Operation “DupeHike” (UNG0902)
Seqrite Labs reported a spear-phishing campaign active since November 2025, targeting Russian corporate employees and delivering:
- an implant called DUPERUNNER
- which is used to load AdaptixC2, a command-and-control framework
The lure involves decoy themes such as:
- employee bonuses
- internal salary policies
- finance-related documents
The infection again uses ZIP archives containing malicious LNK files. A decoy PDF is displayed while system profiling and beacon deployment happens quietly.
Paper Werewolf / GOFFEE: AI decoys + XLL add-ins
Another group, known as Paper Werewolf (GOFFEE), has reportedly used:
- AI-generated decoy files
- DLLs compiled into Excel add-ins (XLL)
This chain delivers a backdoor known as EchoGather, which:
- collects system details
- connects to a hardcoded C2 server
- supports command execution and file transfer
- uses HTTP(S) communications through the WinHTTP API

