Cybersecurity researchers are warning about a new attack campaign where threat actors are using stolen credentials to install legitimate Remote Monitoring and Management (RMM) tools, giving them stealthy and persistent remote control over victim systems.
Instead of relying on traditional malware or custom backdoors, the attackers are taking advantage of trusted IT software that many organizations already use. Researchers say the strategy is simple but effective: steal access first, then use approved remote admin tools to stay inside the network.

Why this method is dangerous
This campaign highlights a growing trend in cybercrime: attackers don’t always need “viruses” anymore. If they can obtain valid credentials, they can bypass many security controls and operate like a trusted administrator.
Once inside, RMM software becomes a powerful weapon because it:
- blends into legitimate IT activity
- enables remote access without needing exploits
- can survive reboots and manual shutdown attempts
- often won’t trigger antivirus alerts
Two-stage attack chain: phishing first, remote access next
The campaign is carried out in two main waves:

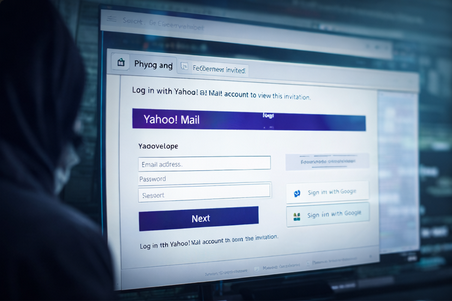
Wave 1: Credential theft using fake invitations
The attackers send phishing emails designed to look like invitations from Greenvelope, a real online invitation platform. These emails contain malicious links that lead victims to fake login pages.
The phishing sites are designed to steal credentials for services such as:
- Microsoft Outlook
- Yahoo Mail
- AOL Mail
Once the victim enters their login details, the attackers capture the credentials and move to the next step.
Wave 2: RMM tool deployment using stolen accounts
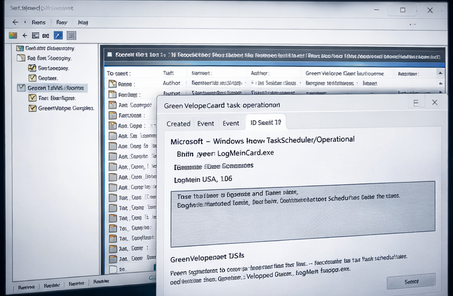
After stealing the email credentials, the threat actor uses the compromised mailbox identity to register or sign in to LogMeIn. This allows them to generate RMM tokens that are later used to deploy remote management software on the victim’s machine.
Researchers observed the follow-up payload delivered through an executable named:
GreenVelopeCard.exe
The file is digitally signed with a valid certificate, which makes it appear trustworthy and reduces suspicion.
Silent install + persistence techniques
The executable includes configuration data (in JSON format) that helps it quietly deploy LogMeIn Resolve (previously known as GoTo Resolve) without alerting the user.
Once installed, the software connects to infrastructure controlled by the attacker, allowing remote access without the victim realizing what has happened.
To strengthen persistence, attackers were also seen:
- modifying the RMM service settings to run with high privileges on Windows
- creating hidden scheduled tasks to automatically relaunch the tool even if the victim shuts it down
This ensures the attacker maintains access over time.
What defenders should do
To reduce exposure, organizations should take the campaign seriously and treat unexpected RMM activity as a potential compromise.
Recommended defense actions include:
- monitor for unauthorized RMM installations
- alert on unusual LogMeIn/Resolve activity across endpoints
- review endpoints for newly created scheduled tasks and suspicious service changes
- enforce MFA and conditional access for email accounts
- tighten software allow-listing rules for admin utilities