Security researchers have uncovered a new social engineering campaign aimed at macOS users that delivers credential-stealing malware through a highly refined version of the ClickFix technique. The operation, dubbed “Matryoshka,” uses multiple layers of hidden code to slip past security defenses and quietly harvest sensitive data.
🎯 Fake “Fix” Prompts Trick Users Into Self-Infection
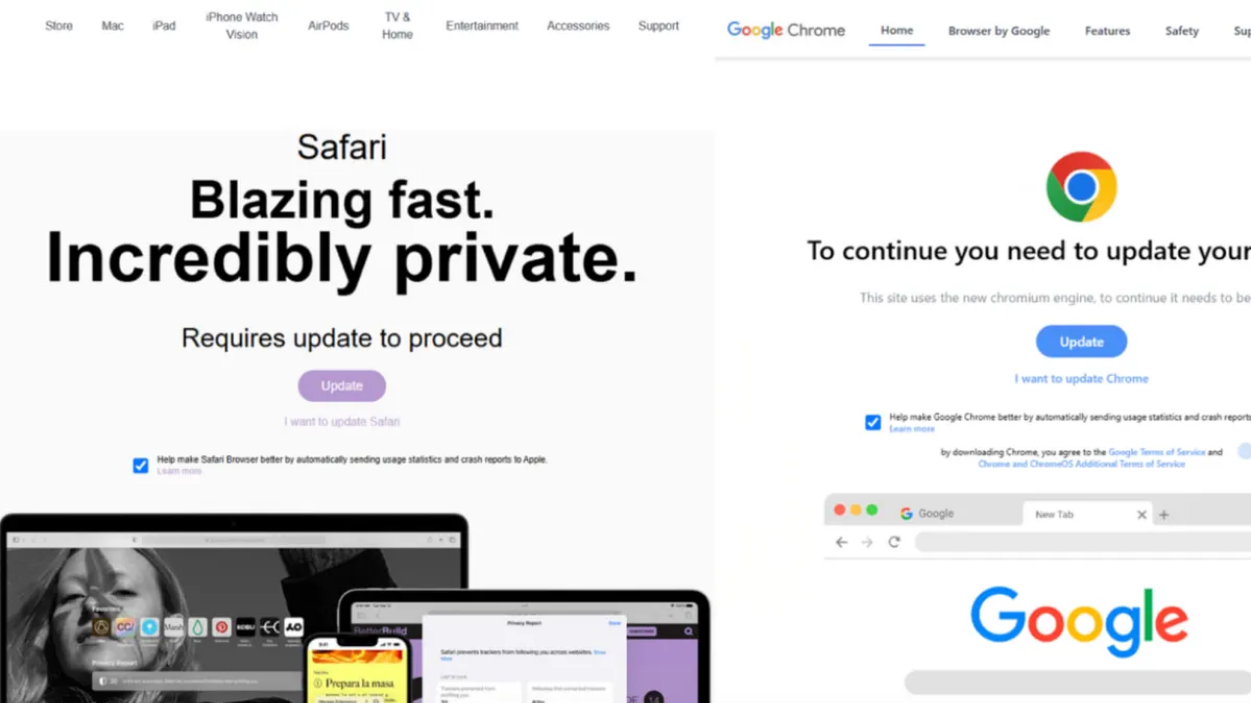
Instead of relying on traditional malware downloads, the attack manipulates victims into running malicious commands themselves. Users are redirected to convincing fake webpages that claim their system needs a quick repair or update.
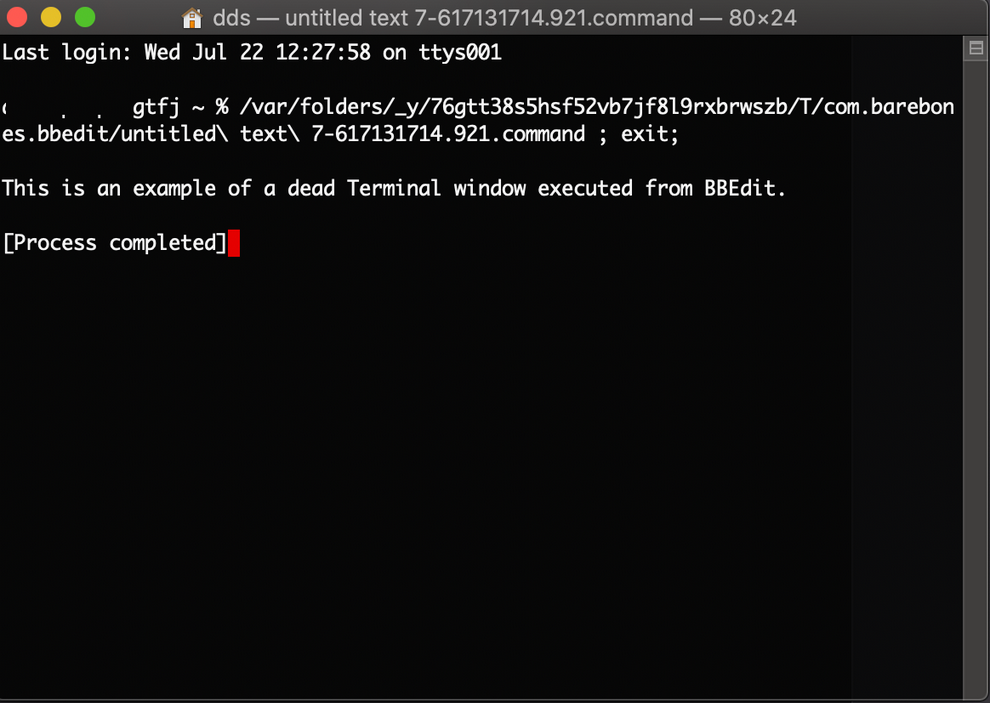
Victims are instructed to copy and paste a command into the macOS Terminal. Because the action appears to be a legitimate troubleshooting step, many users comply without realizing they are executing harmful code.
This approach bypasses common security habits, such as avoiding unknown downloads, since no obvious file installation occurs.
🌐 Typosquatting Used to Capture Victims
Attackers lure users by registering web addresses that closely resemble legitimate sites. A single extra letter or slight misspelling is enough to divert traffic from real software resources to malicious clones.
Once on the fraudulent page, visitors encounter instructions designed to appear technical and trustworthy, increasing the likelihood that they will follow them.
🧠 Multi-Layered Obfuscation Hides the Payload
The Matryoshka variant earns its name from the way its malicious components are nested within one another. The harmful code remains encoded and compressed until it runs in memory, avoiding the creation of obvious files on disk.
Because many security tools rely on scanning stored files, this memory-only execution makes detection significantly more difficult.
After activation, the loader retrieves additional scripts that expand the attack.

🔐 Focus on Credentials and Cryptocurrency
The malware’s primary goal is data theft. It targets browser logins, stored credentials, and cryptocurrency wallets, particularly applications used to manage digital assets.
If automated extraction fails, the malware resorts to deceptive pop-up windows that repeatedly request passwords under the guise of legitimate system prompts.
This tactic increases the chances of capturing credentials even from cautious users.
🕵️ Stealth Techniques Keep the Attack Hidden
The infection process unfolds in several stages designed to minimize suspicion:
- The command runs in the background and quickly exits
- Terminal output is suppressed so nothing unusual appears
- Malicious activity occurs silently in memory
- Communication with attacker servers uses specialized request patterns
These measures help the attack blend into normal system activity and evade automated scanning tools.
⚠️ Why macOS Users Are Increasingly Targeted
As Apple devices gain popularity in professional environments and among cryptocurrency users, attackers are investing more effort into macOS-specific threats. The long-standing belief that Macs are largely immune to malware is no longer accurate.
Modern campaigns focus heavily on social engineering, exploiting user trust rather than technical vulnerabilities.
🛡️ How to Protect Yourself
Security experts recommend several precautions:
- Never paste commands from websites into Terminal
- Verify website addresses carefully before following instructions
- Use official update mechanisms for software installations
- Enable system protections and keep devices updated
- Be cautious of unexpected prompts requesting passwords
Organizations should also monitor unusual Terminal activity and block suspicious domains that mimic legitimate services.
🔎 Bottom Line
The Matryoshka campaign demonstrates how cybercriminals are evolving beyond traditional malware delivery methods. By convincing users to execute malicious commands themselves, attackers can bypass many built-in defenses and quietly steal valuable data.
Awareness and caution remain the strongest defenses against this type of threat.