Security researchers have uncovered an active malware campaign that is abusing a DLL side-loading weakness in a legitimate Windows executable linked to the open-source c-ares library. The technique allows attackers to quietly bypass security defenses and install a broad range of common trojans and information stealers.
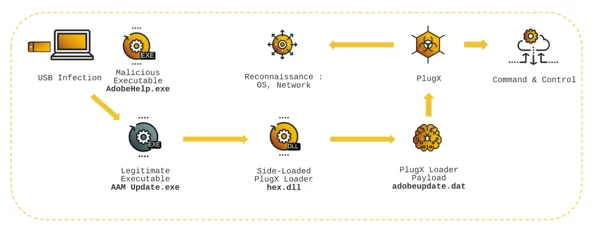
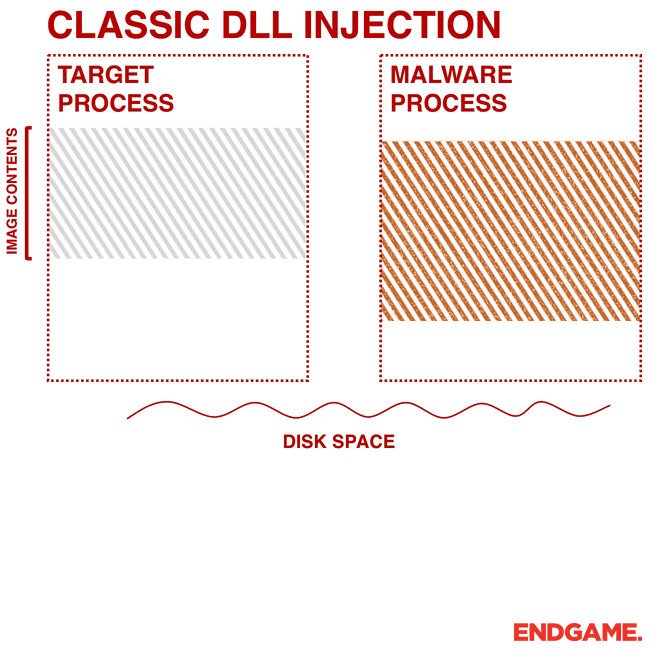
According to findings shared by Trellix, attackers bundle a malicious libcares-2.dll file with a legitimate, digitally signed executable called ahost.exe. By placing the rogue DLL in the same directory, the attackers exploit Windows’ DLL search order behavior, causing the malicious file to load instead of the real library. Because the executable is trusted and signed, many traditional security tools fail to flag the activity.
The campaign has been observed delivering multiple well-known malware families, including Agent Tesla, CryptBot, Formbook, Lumma Stealer, Vidar Stealer, Remcos RAT, Quasar RAT, DCRat, and XWorm. These payloads enable credential theft, system surveillance, and long-term remote access.
Who Is Being Targeted
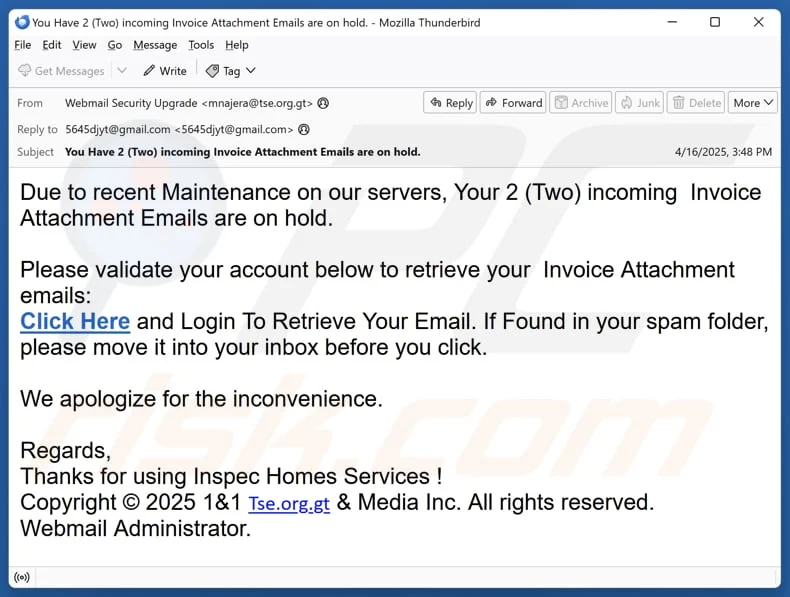
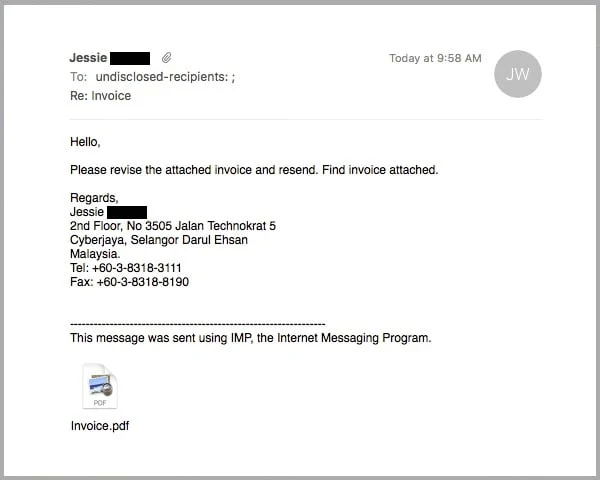
Victims appear to be employees working in finance, procurement, supply chain, and administrative roles across commercial and industrial sectors such as oil and gas, import, and export businesses. Attack messages are written in several languages, including Arabic, Spanish, Portuguese, Farsi, and English, suggesting a geographically focused but multi-regional campaign.
How the Attack Works
The operation relies on a signed version of ahost.exe, a file commonly distributed with the desktop application from GitKraken. Threat actors often rename the file to appear harmless and pair it with a weaponized DLL. Once executed, the binary loads the malicious library, giving attackers full code execution without raising immediate suspicion.
Samples uploaded to VirusTotal show the file masquerading as invoices and business documents. Examples include filenames like “RFQ_NO_04958_LG2049 pdf.exe,” “OVERDUE.INV.PDF.exe,” and “Fatura da DHL.exe,” all designed to trick users into opening what looks like a legitimate attachment.
Researchers warn that this technique highlights a growing trend where attackers rely on trusted, signed software to quietly deploy malware while evading signature-based detection.
Parallel Rise in Advanced Phishing Campaigns
At the same time, Trellix has reported a sharp increase in phishing attacks targeting Facebook users using a Browser-in-the-Browser technique. This method creates a fake login pop-up inside a real browser window, making it extremely difficult for victims to tell the difference between a real and fraudulent authentication screen.
In many cases, victims receive phishing emails posing as legal notices, copyright complaints, or security alerts. These messages often include shortened links that redirect users to fake Meta CAPTCHA pages before triggering the counterfeit login window.
The phishing infrastructure frequently relies on legitimate cloud platforms such as Netlify and Vercel, helping the attackers bypass email and web filtering systems. Evidence suggests these campaigns may have been active since mid-2025.
AsyncRAT Delivered Through Cloudflare and Python Payloads
Researchers have also tied recent activity to a multi-stage phishing operation that delivers AsyncRAT using Python-based payloads and temporary tunnels created through Cloudflare. The infection chain begins with a ZIP file hosted on Dropbox, containing an internet shortcut that launches malicious scripts.
Analysis by Forcepoint and Trend Micro shows the attackers using Windows Script Host, PowerShell, and other built-in tools to avoid detection. The scripts install a Python environment, establish persistence, inject AsyncRAT into explorer.exe, and display a decoy PDF to distract the victim.
Why This Matters
Across these campaigns, a common theme emerges: attackers are increasingly abusing trusted software, signed binaries, open-source tools, and legitimate cloud services to hide malicious activity in plain sight. By blending into normal user behavior and infrastructure, these threats are harder to detect and easier to scale.
Security teams are advised to closely monitor DLL loading behavior, restrict execution of renamed binaries, inspect cloud-hosted phishing pages, and improve visibility into living-off-the-land techniques that rely on native Windows tools and trusted platforms.