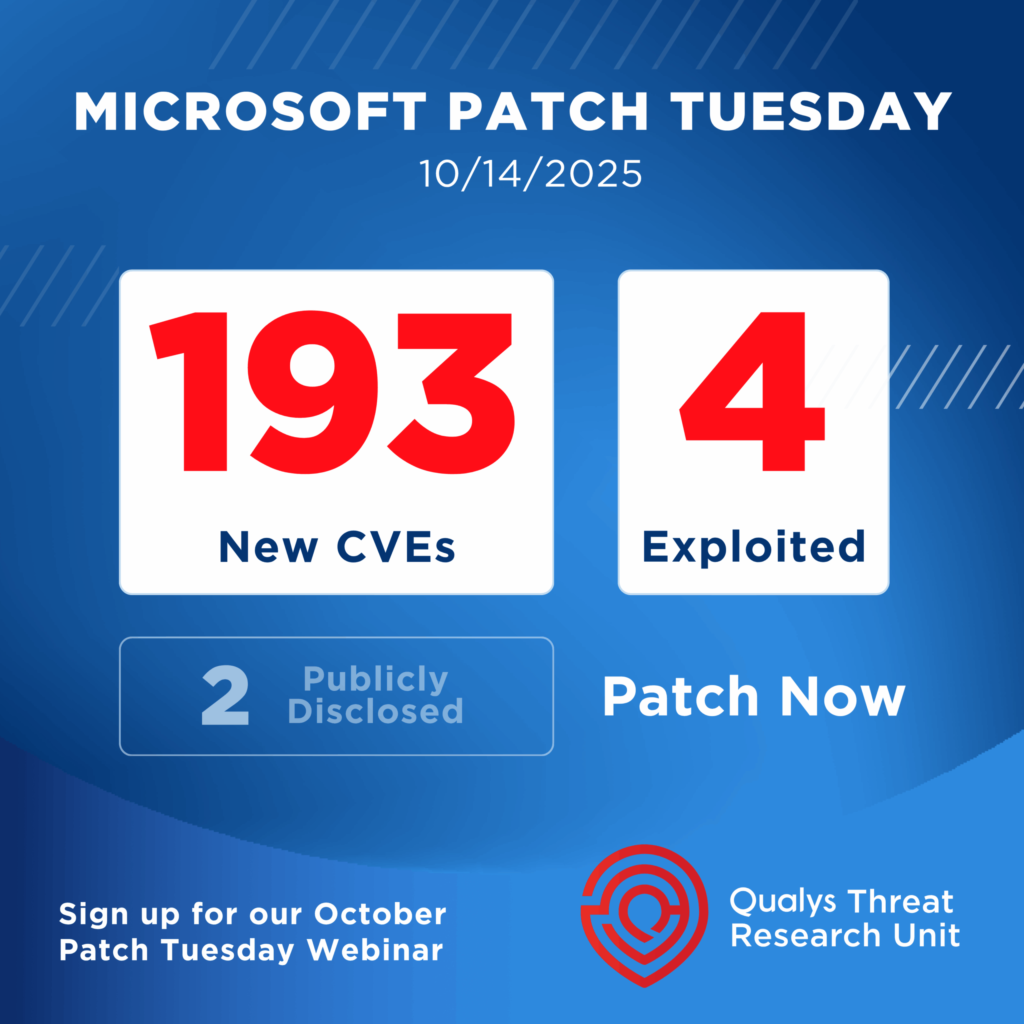
Microsoft has released its first Patch Tuesday updates for 2026, rolling out fixes for 114 security vulnerabilities across Windows and related products. One of the flaws, the company confirmed, is already being exploited in real-world attacks.
Of the total issues addressed, eight are rated Critical and 106 are classified as Important. Privilege escalation bugs dominate this month’s release, accounting for more than half of the patched flaws. Remote code execution and information disclosure issues also feature heavily. Patch analysts note that this update ranks among the largest January releases Microsoft has ever issued.
Actively Exploited Windows Flaw
The most urgent issue is CVE-2026-20805, an information disclosure vulnerability in Windows Desktop Window Manager (DWM) with a CVSS score of 5.5. Microsoft says the bug allows a locally authenticated attacker to leak sensitive memory-related information.
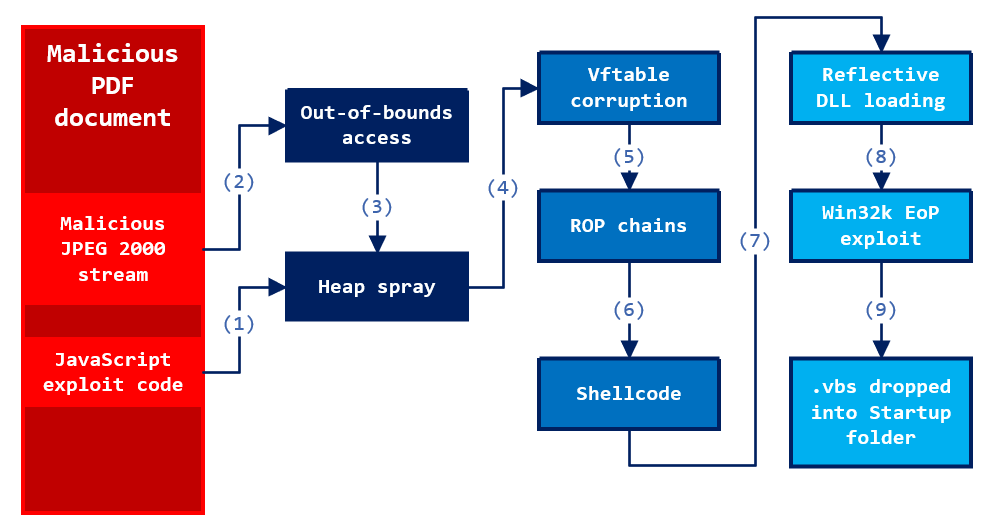
While technical details remain limited, the flaw exposes memory address data tied to Windows’ internal communication mechanisms. Security researchers warn that even “low-severity” information leaks like this can be dangerous when chained with other vulnerabilities.
Desktop Window Manager plays a central role in rendering everything displayed on a Windows system, making it a frequent target for attackers. Researchers note that weaknesses in DWM are often leveraged to weaken memory protections such as Address Space Layout Randomization (ASLR), paving the way for more reliable exploits.
The flaw has been added to the Known Exploited Vulnerabilities catalog by CISA, requiring U.S. federal agencies to apply the patch by early February 2026.
History of DWM Exploitation
This is not the first time DWM has been abused in active attacks. In 2024, a separate DWM vulnerability was used by multiple threat groups to escalate privileges as part of malware campaigns. Security researchers describe DWM as a recurring focus during Patch Tuesday due to its deep integration with the operating system and broad attack surface.
Secure Boot and Driver Cleanup
Another notable fix addresses a Secure Boot security feature bypass tracked as CVE-2026-21265. The issue could allow attackers to undermine the mechanism that ensures only trusted firmware and boot components are loaded during system startup.
Microsoft also reiterated its plan to retire several legacy Secure Boot certificates issued in 2011, beginning in mid-2026. Organizations that fail to update to newer certificates risk boot failures or weakened protections, especially in enterprise environments.
In addition, the update removes vulnerable legacy modem drivers that shipped with Windows. These drivers were found to be susceptible to privilege escalation attacks that could allow attackers to gain SYSTEM-level access. Microsoft previously removed similar drivers in late 2025 after evidence of exploitation in the wild.
High-Risk Privilege Escalation in VBS
Security teams are also being urged to prioritize CVE-2026-20876, a privilege escalation flaw affecting Windows Virtualization-Based Security (VBS) Enclave. The vulnerability could allow attackers with existing access to elevate privileges into one of Windows’ most trusted execution layers.
Although exploitation requires a foothold on the system, the impact is severe. Researchers warn that compromising VBS undermines core Windows security boundaries, enabling stealthy persistence and evasion of advanced defenses.
Edge and Other Fixes
Outside of Windows, Microsoft has already patched additional vulnerabilities in its Edge browser since the December 2025 update, including flaws affecting Android and Chromium components.
Broader Patch Activity Across the Industry
Microsoft’s update lands alongside a wave of January security releases from dozens of other vendors, spanning cloud services, networking hardware, operating systems, and enterprise software. Security teams are being advised to review all relevant advisories and prioritize patches based on exposure and exploit activity.
What Organizations Should Do
Microsoft recommends applying the January 2026 updates as soon as possible, especially on systems exposed to untrusted users or running sensitive workloads. With one vulnerability already under active exploitation and several others capable of breaking core security protections, delayed patching significantly increases risk.