Ivanti has released emergency security updates for two critical vulnerabilities affecting Ivanti Endpoint Manager Mobile (EPMM) after confirming the flaws have been exploited in real-world zero-day attacks.
One of the vulnerabilities has also been added to the CISA Known Exploited Vulnerabilities (KEV) catalog, increasing urgency for organizations that rely on Ivanti EPMM to manage enterprise mobile devices.
What’s Vulnerable
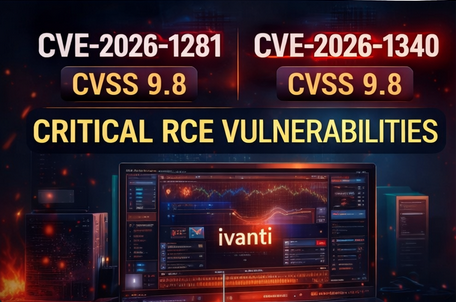
Ivanti disclosed two critical code injection flaws, both rated CVSS 9.8, which can allow unauthenticated remote code execution (RCE) — meaning attackers can potentially run commands on the appliance without valid login credentials.
The vulnerabilities are:
- CVE-2026-1281 (CVSS 9.8) – code injection → unauthenticated RCE
- CVE-2026-1340 (CVSS 9.8) – code injection → unauthenticated RCE
Ivanti said the issues specifically impact features tied to:
- In-House Application Distribution
- Android File Transfer Configuration
The company also clarified that these flaws do not impact other Ivanti products such as:
- Ivanti Neurons for MDM
- Ivanti Endpoint Manager (EPM)
- Ivanti Sentry
Affected Versions
According to Ivanti, multiple EPMM versions are affected, including:
- EPMM 12.5.0.0 and earlier
- EPMM 12.6.0.0 and earlier
- EPMM 12.7.0.0 and earlier
- EPMM 12.5.1.0 and earlier
- EPMM 12.6.1.0 and earlier
Ivanti released interim fixes through RPM updates:
- fixes delivered via RPM 12.x.0.x
- fixes delivered via RPM 12.x.1.x
Important note for admins
Ivanti warned that the RPM patch does not carry over during version upgrades, meaning if you upgrade your appliance to a newer version, you must reapply the RPM fix.
Ivanti plans to permanently resolve the issues in EPMM 12.8.0.0, expected later in Q1 2026.
Real-World Exploitation Confirmed
Ivanti acknowledged that a small number of customers were exploited at the time of disclosure.
However, the company said it does not currently have enough consistent attacker behavior to publish “reliable atomic indicators,” meaning defenders may not have simple signatures or IOCs to detect activity immediately.
Why This Is Serious
Ivanti noted that successful exploitation gives the attacker arbitrary code execution on the appliance.
This is especially dangerous because EPMM appliances often sit at the center of mobile enterprise operations and may contain:
- sensitive configuration data
- mobile device management details
- access paths into internal environments (supporting lateral movement)
Ivanti also said previous EPMM attacks commonly used:
- web shells
- reverse shells
…to maintain persistence after exploitation.
How to Hunt for Exploitation
Ivanti recommends reviewing Apache access logs here:
/var/log/httpd/https-access_log
They also provided a detection regex pattern aimed at spotting suspicious exploitation attempts tied to the affected endpoints:
^(?!127\.0\.0\.1:\d+
.*$).*?\/mifs\/c\/(aft|app)store\/fob\/.*?404
What to look for
Ivanti explains that:
- legitimate use typically returns HTTP 200
- exploitation attempts tend to generate HTTP 404 entries

Additional Checks: Signs of Abuse
Ivanti advises customers to review EPMM settings closely for unusual or unauthorized changes, including:
- new or modified admin accounts
- SSO / LDAP authentication configuration changes
- new push applications sent to devices
- unusual modifications to in-house apps
- new or edited security policies
- network/VPN config changes pushed to mobile devices
If Compromised: What to Do
If evidence of compromise is found, Ivanti recommends rebuilding or restoring the appliance using a known-good backup, or replacing the appliance entirely, then migrating clean data.
After recovery, Ivanti urges organizations to lock things down by:
- resetting all local EPMM passwords
- resetting LDAP and/or KDC lookup service accounts
- revoking and replacing EPMM certificates
- resetting passwords for any internal/external service accounts tied to EPMM
CISA KEV Deadline
CISA added CVE-2026-1281 to its Known Exploited Vulnerabilities catalog, requiring U.S. Federal Civilian Executive Branch (FCEB) agencies to patch by:
✅ February 1, 2026
Even if you’re not a federal agency, a KEV listing is usually a strong sign that exploitation is active and scalable.