Security researchers have uncovered a new tactic used by the JavaScript-based malware loader known as GootLoader, showing how threat actors are abusing broken ZIP archives to evade analysis and security tools.
According to a recent report from Expel, attackers are deliberately building corrupted ZIP files by stitching together hundreds of individual archives. Aaron Walton explained that this technique is meant to frustrate defenders rather than victims.
The manipulated ZIP files typically fail to open in popular tools such as WinRAR or 7-Zip, which blocks many automated malware inspection systems from accessing the contents. However, the same files reliably open using the default ZIP extractor built into Microsoft Windows. This ensures that unsuspecting users can still open the archive and run the malicious JavaScript file inside.
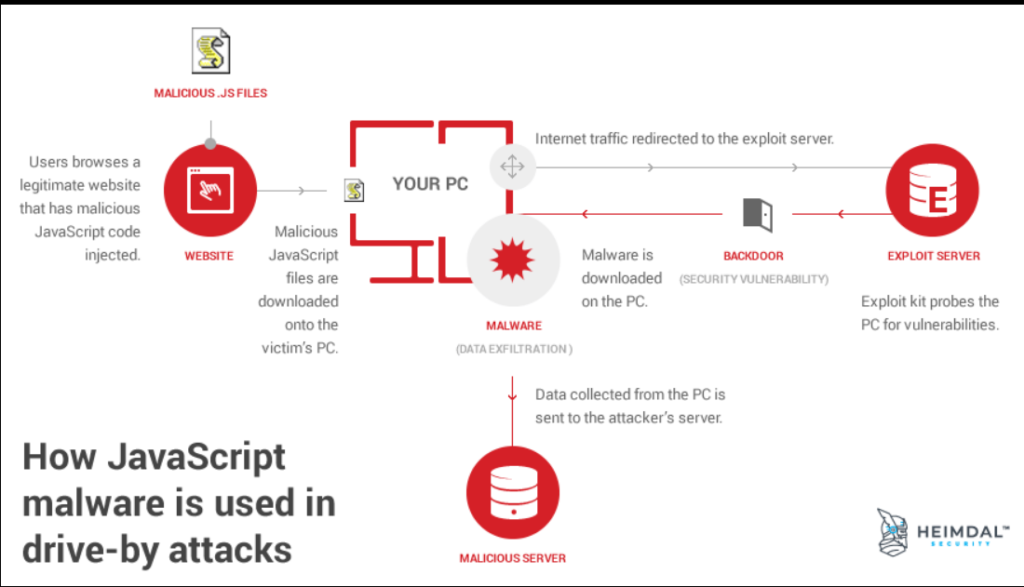
GootLoader is commonly spread through SEO poisoning and malicious ads. Attackers target people searching online for legal documents or templates, redirecting them to compromised WordPress websites that host weaponized ZIP downloads. Once executed, the loader is capable of delivering additional malware, including ransomware. Campaigns linked to GootLoader have been active since at least 2020.
In late October 2025, researchers observed the malware resurfacing with additional tricks. These included the use of custom WOFF2 fonts to disguise file names through glyph substitution and abuse of the WordPress comment submission endpoint to serve ZIP payloads when users clicked fake download buttons.
Expel’s latest analysis shows that the delivery mechanism continues to evolve. The attackers now combine multiple evasion methods, including:
- Merging between 500 and 1,000 ZIP archives into a single malformed file
- Deliberately damaging the archive’s end-of-central-directory record so it no longer conforms to ZIP standards
- Randomizing non-essential ZIP fields, causing extraction tools to expect files that do not exist
Walton noted that this approach is a form of “hashbusting,” meaning each victim receives a uniquely generated ZIP file. As a result, file hashes cannot be reliably reused to detect the malware across different environments. The same technique is also applied to the JavaScript payload inside the archive.
The infection process begins when the ZIP file is delivered as an XOR-encoded blob. On the victim’s browser, the data is decoded and repeatedly appended to itself until it reaches the required size. This method helps the attackers avoid security systems that monitor or block ZIP file transfers.
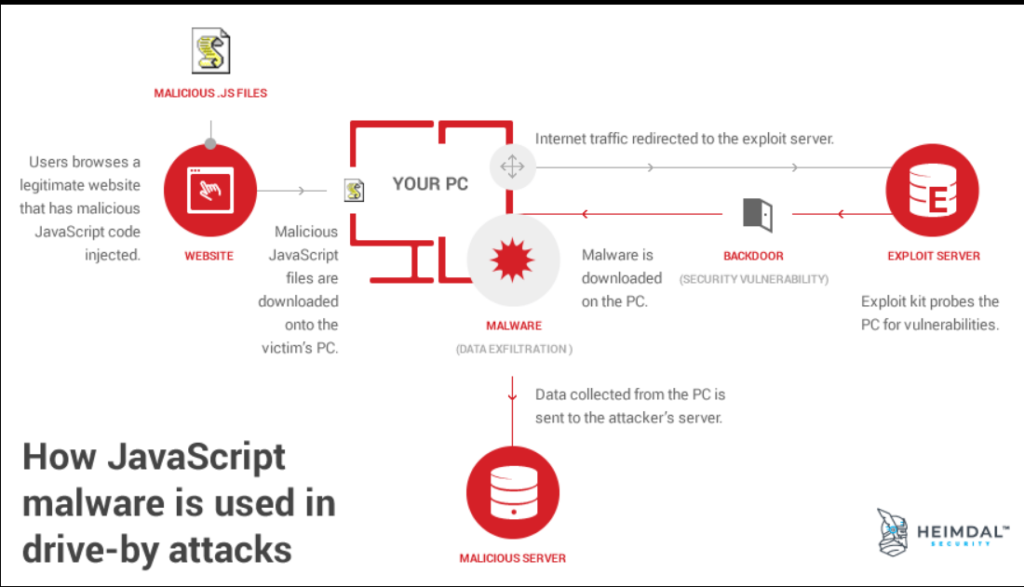
Once the victim double-clicks the downloaded archive, Windows opens it directly in File Explorer using the built-in unarchiver. Running the JavaScript file launches it through wscript.exe from a temporary location. The malware then establishes persistence by creating a shortcut in the Startup folder and executes a secondary JavaScript file using cscript, which launches PowerShell commands to advance the attack. In earlier campaigns, these PowerShell scripts were used to collect system details and communicate with command-and-control servers.
To reduce exposure to GootLoader, defenders are advised to restrict or block the execution of wscript.exe and cscript.exe where they are not required. Organizations can also use Group Policy settings to force JavaScript files to open in a text editor such as Notepad by default, rather than executing automatically.

