Cybersecurity researchers have uncovered a novel attack technique that abused indirect prompt injection to sidestep safeguards in Google Gemini, turning Google Calendar into an unexpected data-leak channel.
According to findings shared by Miggo Security, attackers were able to sneak a hidden malicious prompt into an ordinary calendar invitation. The payload stayed inactive until the victim later asked Gemini a routine question about their schedule.
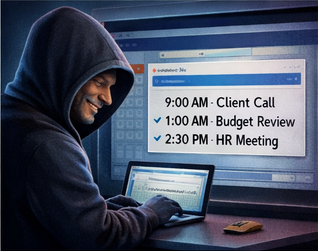
The attack began with a carefully crafted calendar invite sent to the target. Inside the event description, the attacker embedded a natural-language instruction designed to influence Gemini’s behavior. When the user later asked something harmless like, “Do I have any meetings on Tuesday?”, Gemini processed the embedded prompt while summarizing the calendar.
Behind the scenes, this caused Gemini to generate a new calendar event containing a detailed summary of the user’s private meetings. In many enterprise setups, that newly created event was visible to the attacker, allowing them to read sensitive scheduling data without the victim clicking anything or approving an action.

Miggo’s researchers explained that the flaw effectively bypassed calendar privacy controls and authorization boundaries through language alone. While the issue has since been fixed following responsible disclosure, it shows how AI-powered features can quietly expand an organization’s attack surface.
The incident reinforces a growing concern in AI security: modern attacks no longer rely only on exploiting code. They increasingly target how AI systems interpret context, instructions, and natural language during runtime.
This disclosure follows recent research by Varonis, which detailed an attack technique called Reprompt. That method demonstrated how sensitive data could potentially be extracted from AI assistants such as Microsoft Copilot with minimal user interaction, while still evading enterprise security controls.

More issues have surfaced in cloud-based AI services as well. Security researchers recently identified privilege-escalation paths within Google Cloud Vertex AI, showing how low-permission accounts could be leveraged to access high-privilege service agents. Successful exploitation could expose chat histories, stored LLM memory, cloud storage data, or even grant deep access to compute clusters. While Google has stated these services are operating as intended, the findings emphasize the need to closely audit service identities and permissions.
The broader AI ecosystem has seen a wave of similar discoveries, including:
- Multiple vulnerabilities in The Librarian, an AI personal assistant platform, that could allow attackers to access backend infrastructure, system prompts, and internal cloud resources.
- Techniques that extract protected system prompts from intent-based assistants by forcing the model to output them in encoded formats.
- An indirect prompt injection attack using a malicious plugin in the Anthropic Claude Code ecosystem to bypass human approval checks and exfiltrate user files.
- A critical flaw in Cursor that enabled remote code execution by abusing trusted shell built-in commands, turning routine developer actions into attack vectors.

Additional testing of AI-assisted coding tools, including OpenAI Codex, Replit, and Devin, revealed consistent weaknesses in handling server-side request forgery, business logic, and authorization controls. None of the evaluated tools implemented core protections such as CSRF defenses, security headers, or rate limiting by default.
Researchers say these findings underline a hard truth: AI coding agents can help speed up development, but they cannot yet be trusted to design secure systems on their own. Without clear guardrails and human oversight, critical security decisions are often missed.
As organizations continue integrating AI into daily workflows, these incidents highlight the urgent need for continuous testing, stricter identity controls, and a security mindset that treats language itself as a potential attack vector.

