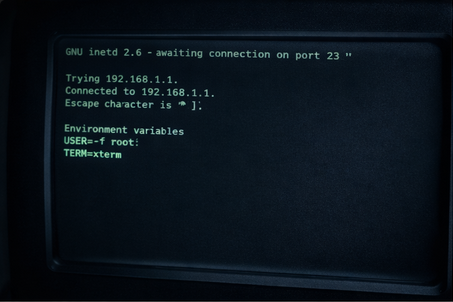
A newly disclosed vulnerability in the GNU InetUtils telnet daemon (telnetd) has raised serious concerns after remaining unnoticed for almost 11 years.
The flaw is tracked as CVE-2026-24061 and carries a CVSS score of 9.8 (Critical). It impacts GNU InetUtils versions 1.9.3 through 2.7, meaning a wide range of systems using the package could be at risk.
What the bug allows
At its core, the issue allows remote authentication bypass, potentially enabling an attacker to gain root access.
The problem stems from how the telnet daemon passes user-supplied data to the system login process. Specifically:
- telnetd launches
/usr/bin/login(typically running with root privileges) - it includes the value of the USER environment variable received from the remote client
- that value is not properly sanitized
An attacker can exploit this weakness by setting the USER value to a specially crafted string such as:
-f root
Since the login program supports the -f option (which can skip authentication under certain conditions), the attacker may be able to log in as root without entering a password.

Timeline and discovery
GNU contributor Simon Josefsson explained that the flaw appears to have been introduced through a source code change in March 2015, later included in the InetUtils 1.9.3 release in May 2015.
The vulnerability was discovered and reported in January 2026 by security researcher Kyu Neushwaistein (also known as Carlos Cortes Alvarez).
Exploitation attempts already observed
Threat intelligence monitoring suggests attackers are already paying attention. Data from GreyNoise indicates that multiple IP addresses have been observed attempting to exploit this authentication bypass in recent activity.
The IPs were linked to locations including:
- Hong Kong
- United States
- Japan
- Netherlands
- China
- Germany
- Singapore
- Thailand
GreyNoise reportedly classified the observed sources as malicious.
How to protect your systems
Organizations and administrators are urged to act quickly.
Recommended actions:
✅ Apply the latest patches for GNU InetUtils immediately
✅ Restrict access to the Telnet port (TCP/23) so only trusted hosts can connect
Temporary workarounds (if patching isn’t immediate):
- Disable telnetd entirely (best option)
- Configure InetUtils telnetd to use a custom login tool that does not support the
-fauthentication bypass option