Fortinet has released security updates to address a high-severity flaw in its FortiSIEM platform that could allow unauthenticated attackers to remotely execute code on affected systems.
The vulnerability, tracked as CVE-2025-64155, carries a CVSS score of 9.4, placing it firmly in the critical category. According to Fortinet, the issue stems from an operating system command injection weakness that can be exploited through specially crafted TCP requests.
Fortinet explained that the flaw allows attackers to execute unauthorized commands without authentication by abusing how FortiSIEM processes certain inputs. The issue affects Super and Worker nodes only and has been fixed in recent releases.

Affected Versions
The following FortiSIEM versions are impacted:
- FortiSIEM 6.7.0–6.7.10 (migration required)
- FortiSIEM 7.0.0–7.0.4 (migration required)
- FortiSIEM 7.1.0–7.1.8 (upgrade to 7.1.9 or later)
- FortiSIEM 7.2.0–7.2.6 (upgrade to 7.2.7 or later)
- FortiSIEM 7.3.0–7.3.4 (upgrade to 7.3.5 or later)
- FortiSIEM 7.4.0 (upgrade to 7.4.1 or later)
FortiSIEM 7.5 and FortiSIEM Cloud are not affected.
How the Exploit Works
The vulnerability was discovered and responsibly disclosed by Zach Hanley, a researcher at Horizon3.ai. According to the researcher, the attack chain combines two weaknesses.
The first issue allows unauthenticated argument injection that results in arbitrary file writes, enabling remote code execution with administrator privileges. The second issue allows attackers to overwrite files in a way that escalates privileges from admin to root, fully compromising the appliance.
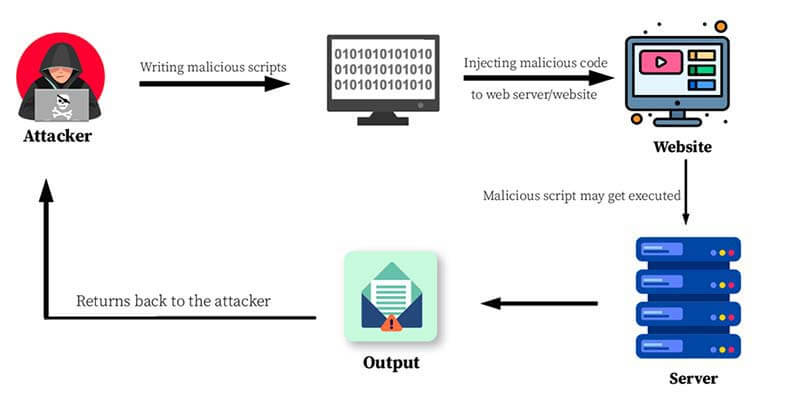
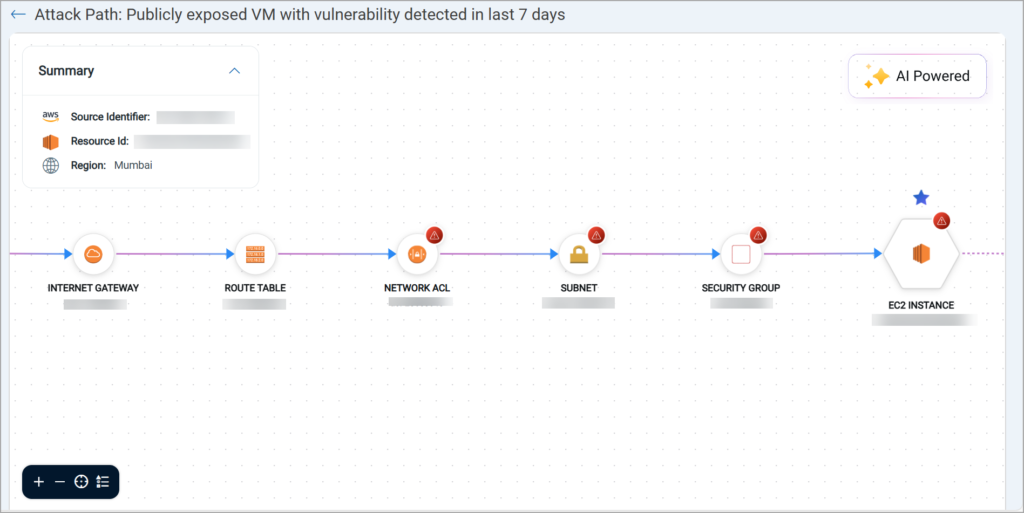
At the center of the problem is FortiSIEM’s phMonitor service, a core backend component responsible for health monitoring, task coordination, and inter-node communication over TCP port 7900. When handling certain logging requests, phMonitor invokes a shell script using parameters that can be controlled by an attacker.
By abusing this behavior, an attacker can inject malicious arguments into a curl command and write arbitrary files to disk as the admin user. This access can then be escalated to full system control.
From Admin to Root Access
Researchers found that attackers can write a reverse shell to a file located at /opt/charting/redishb.sh. This file is writable by the admin user and is automatically executed every minute by a root-level cron job. Once the malicious file is in place, the attacker gains root access, effectively taking over the FortiSIEM appliance.
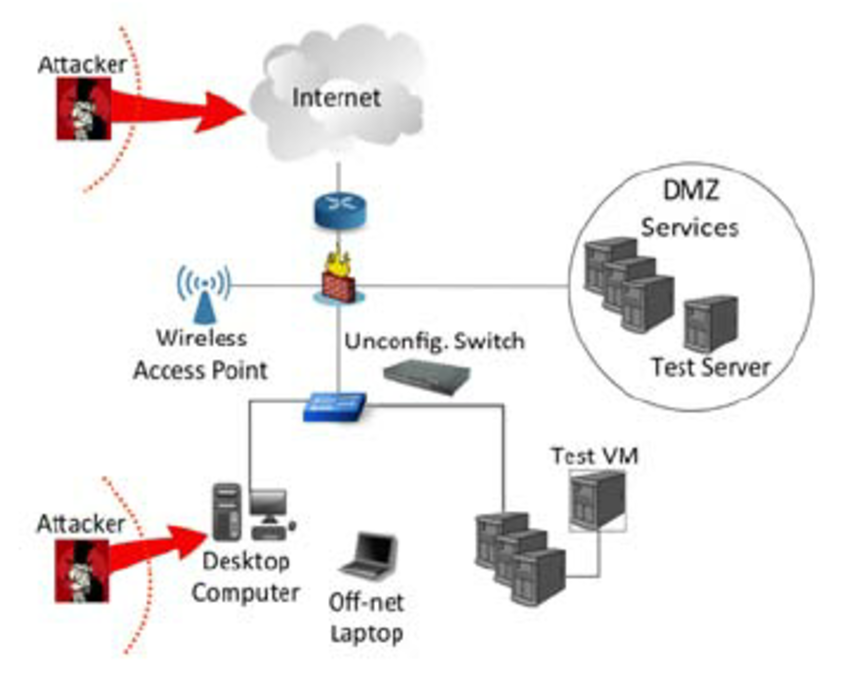
A key concern highlighted in the disclosure is that several phMonitor command handlers are exposed without authentication. Any attacker who can reach port 7900 over the network can potentially invoke these functions.
Additional Fortinet Patch Issued
In a separate advisory, Fortinet also fixed another critical vulnerability affecting FortiFone, tracked as CVE-2025-47855 with a CVSS score of 9.3. This flaw could allow unauthenticated attackers to retrieve device configuration data through crafted HTTP or HTTPS requests to the web portal.
Affected FortiFone versions include:
- FortiFone 3.0.13–3.0.23 (upgrade to 3.0.24 or later)
- FortiFone 7.0.0–7.0.1 (upgrade to 7.0.2 or later)
FortiFone 7.2 is not impacted.
What Users Should Do
Fortinet strongly recommends upgrading to patched versions as soon as possible. As a temporary mitigation for CVE-2025-64155, organizations are advised to restrict network access to TCP port 7900 to trusted systems only.
The disclosures highlight how exposed management services and unauthenticated command handlers can turn monitoring platforms into high-value targets, reinforcing the need for strict network segmentation and timely patching in enterprise environments.